How many patents does
Fireeye have?
Buy the report
The report contains ten-year analysis with the following sections
- patent filing analysis
- worldwide filing analysis
- patent family analysis
- application analysis
- granted analysis
- classification analysis
- citation analysis
contact us for pricing
- VAT will apply to UK companies
- EU companies must supply their VAT number
Check out our sample pages |
Find companies to compare
Many companies now available
Search to find companies of interest
read summary of their published patent
the following tables are just extracts from the report
the company report contains more information
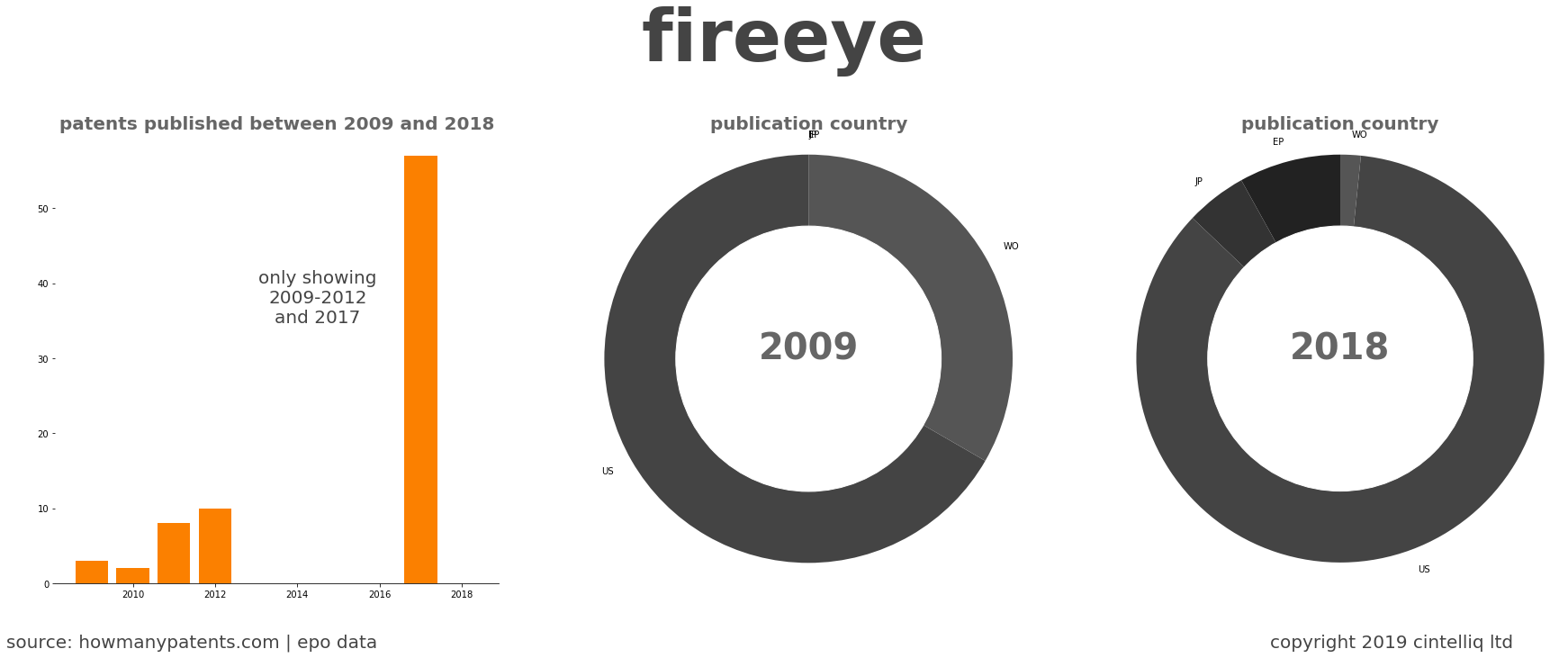
Fireeye
Top ten assignees appearing on patents
2009 - 2018
| fireeye | 247 |
| mandiant | 19 |
| isight partners | 9 |
| invotas cyber solutions | 3 |
| csg cyber solutions | 3 |
| invotas cybr solutions | 1 |
2009
| isight partners | 2 |
2018
| fireeye | 59 |
Fireeye
The top ten patent families are
|
Title of patent family (most common patent title) |
Family members |
Filing year |
|---|---|---|
| heuristic based capture with replay to virtual machine | 39 | 2004 |
| systems and methods for detecting malicious pdf network content | 11 | 2008 |
| exploit detection system with threat-aware microvisor | 11 | 2014 |
| system and method to create a number of breakpoints in a virtual machine via virtual mac… 🛈 | 9 | 2012 |
| optimized resource allocation for virtual machines within a malware content detection sy… 🛈 | 7 | 2013 |
| system and method for detecting executable machine instructions in a data stream | 7 | 2009 |
| system, apparatus and method for automatically verifying exploits within suspect objects… 🛈 | 7 | 2013 |
| system and method employing structured intelligence to verify and contain threats at end… 🛈 | 6 | 2013 |
| malware detection based on vm behavioral analysis and machine learning classification | 6 | 2013 |
| method and system for collecting and organizing data corresponding to an event | 6 | 2008 |